MICROSOFT’S September 2016 PATCH RELEASES

Well after a horrible last month for patches causing issues (KB3176934 breaks Windows 10 Powershell , KB3179575 causing authentication issues with Windows 2012 servers, and KB3177725 & KB3176493 causing printing issues), we are all hoping that this month’s release doesnt cause any problems. If you want to avoid issues with patch deployment, and to facilitate a quick roll back should any windows update causes an issue, remove the patching risk using SnaPatch Patch Management Software. (Also, since you are here, check out the other software we offer)
There are quite a few more than the average Patch Tuesday release. In fact, 14 new Patch Tuesday updates / patches have been released by Microsoft for the August 2016 Update deployment.
MS16-104 – Critical
Cumulative Security Update for Internet Explorer (3183038)
This security update resolves vulnerabilities in Internet Explorer. The most severe of the vulnerabilities could allow remote code execution if a user views a specially crafted webpage using Internet Explorer. An attacker who successfully exploited the vulnerabilities could gain the same user rights as the current user. If the current user is logged on with administrative user rights, an attacker could take control of an affected system. An attacker could then install programs; view, change, or delete data; or create new accounts with full user rights.
MS16-105 – Critical
Security Update for Microsoft Graphics Component (3185848)
This security update resolves vulnerabilities in Microsoft Windows. The most severe of the vulnerabilities could allow remote code execution if a user either visits a specially crafted website or opens a specially crafted document. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights.
MS16-106 – Critical
Security Update for Microsoft Graphics Component (3177393)
This security update resolves vulnerabilities in Microsoft Windows, Microsoft Office, Skype for Business, and Microsoft Lync. The vulnerabilities could allow remote code execution if a user either visits a specially crafted website or opens a specially crafted document. Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights.
MS16-107 – Critical
Security Update for Microsoft Office (3185852)
This security update resolves vulnerabilities in Microsoft Office. The most severe of the vulnerabilities could allow remote code execution if a user opens a specially crafted Microsoft Office file. An attacker who successfully exploited the vulnerabilities could run arbitrary code in the context of the current user. Customers whose accounts are configured to have fewer user rights on the system could be less impacted than those who operate with administrative user rights.
MS16-108 – Critical
Security Update for Microsoft Exchange Server (3185883)
This security update resolves vulnerabilities in Microsoft Exchange Server. The most severe of the vulnerabilities could allow remote code execution in some Oracle Outside In libraries that are built into Exchange Server if an attacker sends an email with a specially crafted attachment to a vulnerable Exchange server.
MS16-109 – Important
Security Update for Silverlight (3182373)
This security update resolves a vulnerability in Microsoft Silverlight. The vulnerability could allow remote code execution if a user visits a compromised website that contains a specially crafted Silverlight application. An attacker would have no way to force a user to visit a compromised website. Instead, an attacker would have to convince the user to visit the website, typically by enticing the user to click a link in either an email or instant message that takes the user to the attacker’s website.
MS16-110 – Important
Security Update for Windows (3178467)
This security update resolves vulnerabilities in Microsoft Windows. The most severe of the vulnerabilities could allow remote code execution if an attacker creates a specially crafted request and executes arbitrary code with elevated permissions on a target system.
MS16-111 – Critical
Security Update for Windows Kernel (3186973)
This security update resolves vulnerabilities in Microsoft Windows. The vulnerabilities could allow elevation of privilege if an attacker runs a specially crafted application on a target system.
MS16-112 – Important
Security Update for Windows Lock Screen (3178469)
This security update resolves a vulnerability in Microsoft Windows. The vulnerability could allow elevation of privilege if Windows improperly allows web content to load from the Windows lock screen.
MS16-113 – Important
Security Update for Windows Secure Kernel Mode (3185876)
This security update resolves a vulnerability in Microsoft Windows. The vulnerability could allow information disclosure when Windows Secure Kernel Mode improperly handles objects in memory.
MS16-114 – Important
Security Update for SMBv1 Server (3185879)
This security update resolves a vulnerability in Microsoft Windows. On Windows Vista, Windows Server 2008, Windows 7, and Windows Server 2008 R2 operating systems, the vulnerability could allow remote code execution if an authenticated attacker sends specially crafted packets to an affected Microsoft Server Message Block 1.0 (SMBv1) Server. The vulnerability does not impact other SMB Server versions. Although later operating systems are affected, the potential impact is denial of service.
MS16-115 – Important
Security Update for Microsoft Windows PDF Library (3188733)
This security update resolves vulnerabilities in Microsoft Windows. The vulnerabilities could allow information disclosure if a user views specially crafted PDF content online or opens a specially crafted PDF document.
MS16-116 – Critical
Security Update in OLE Automation for VBScript Scripting Engine (3188724)
This security update resolves a vulnerability in Microsoft Windows. The vulnerability could allow remote code execution if an attacker successfully convinces a user of an affected system to visit a malicious or compromised website. Note that you must install two updates to be protected from the vulnerability discussed in this bulletin: The update in this bulletin, MS16-116, and the update in MS16-104.
MS16-117 – Critical
Security Update for Adobe Flash Player (3188128)
This security update resolves vulnerabilities in Adobe Flash Player when installed on all supported editions of Windows 8.1, Windows Server 2012, Windows Server 2012 R2, Windows RT 8.1, and Windows 10.
Now that you have made it this far, a quick shameless plug for our software portfolio. 🙂
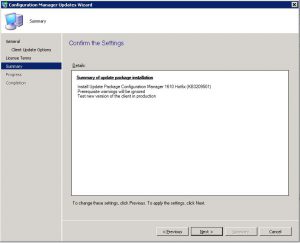
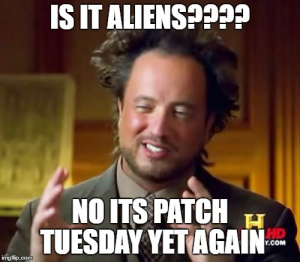
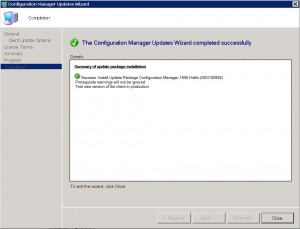
SnaPatch – Patch Management Addon for Microsoft’s SCCM.
SnapShot Master – Take control of your virtual machine snapshots, works with both Hyper-V and Vmware.
Azure Virtual Machine Scheduler – Save money and schedule the shutdown and power on of your virtual machines within Microsoft’s Azure Cloud.
Azure Virtual Machine Deployer – Deploy VMs to Microsoft’s Azure cloud.